In October 2025, the European Commission published its Cloud Sovereignty Framework — an eight-objective blueprint for how EU institutions should procure cloud services, accompanied by a €180 million tender that explicitly required compliance with sovereignty criteria. The document reads like a declaration of independence. Not from a colonial power in the traditional sense, but from an infrastructure dependency that European policymakers have come to view as every bit as threatening: the near-total dominance of American technology corporations over the storage, processing, and flow of European data. Three months later, a white paper from CMS Law — one of Europe’s largest law firms — attempted to calm the waters, arguing that data sovereignty is “not, by default, incompatible” with using US-based service providers. The very fact that such reassurance was necessary tells you everything about the state of digital geopolitics in 2026. Something fundamental has shifted. Data — who stores it, who can access it, and under whose laws it falls — has become the central battleground of twenty-first-century sovereignty. And the nations losing that battle are starting to fight back.
EU sovereign cloud tender, October 2025
Countries with some form of data localization laws
Estimated value of cross-border data flows by 2030
Eyes in the Five Eyes intelligence-sharing alliance
I. The Infrastructure of Extraction
The mechanics of data imperialism are deceptively simple. When a hospital in Nairobi stores patient records on Amazon Web Services, a government ministry in Jakarta runs its email through Microsoft 365, or a bank in São Paulo processes transactions through Google Cloud, the data in each case physically resides on servers controlled by a corporation headquartered in the United States and subject to US law. The users of these services — and the citizens whose data they contain — may never know where their information is stored, who has access to it, or under what legal regime it can be compelled.
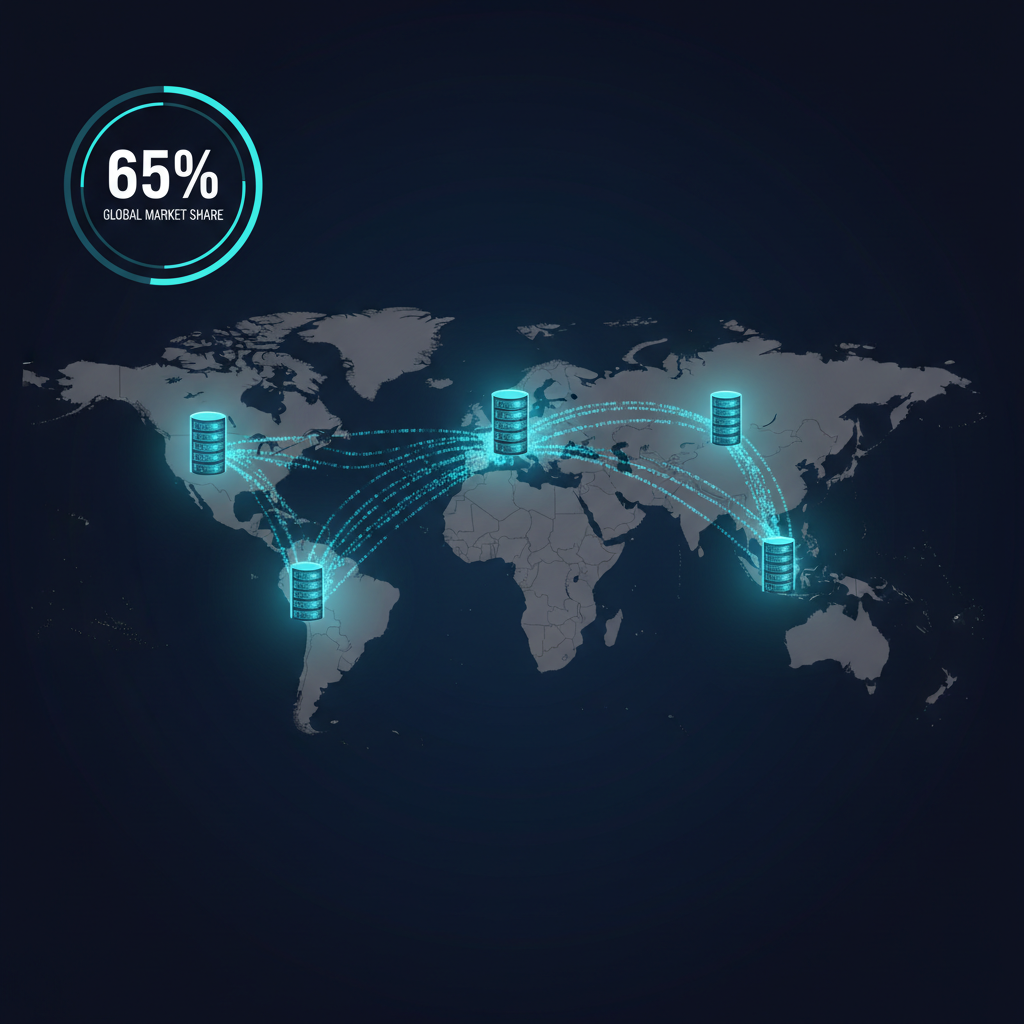
This is not a conspiracy. It is the natural consequence of a market that rewards scale, early-mover advantage, and massive capital investment. Amazon, Microsoft, and Google collectively control approximately 65% of the global cloud infrastructure market. In the Global South — where local alternatives are underfunded and governments lack the technical capacity to build competitive infrastructure — that dominance can exceed 80%. The result is a global information architecture in which the most sensitive data of most nations physically resides under the jurisdiction of a single country.
The term “data imperialism” is deliberately provocative, and not everyone accepts its premises. Proponents of the current system argue that US cloud providers offer superior security, reliability, and cost efficiency compared to local alternatives — and that data, unlike physical territory, can be encrypted, access-controlled, and contractually protected regardless of where it is stored. These arguments have merit. What they don’t address is the asymmetry of power inherent in the arrangement.
II. The Legal Architecture: The CLOUD Act and Its Consequences
The legal framework that makes data imperialism possible has a name: the Clarifying Lawful Overseas Use of Data Act, signed into law in March 2018. Known as the CLOUD Act, it grants US law enforcement the authority to compel American technology companies to produce data stored anywhere in the world, regardless of where that data is physically located or whose data it is.

The Act was passed to resolve a legitimate legal ambiguity. In 2013, the US Department of Justice obtained a warrant for email records held by Microsoft. Microsoft stored the relevant data on servers in Ireland and refused to comply, arguing that US warrants should not have extraterritorial reach. The case, United States v. Microsoft Corp., wound its way to the Supreme Court before the CLOUD Act rendered it moot by explicitly granting the extraterritorial authority that the DOJ had claimed.
The CLOUD Act also established a framework for bilateral “executive agreements” that allow partner nations to request data directly from US technology companies. The first such agreement was signed with the United Kingdom in 2019 and entered into force in 2022. A second, with Australia, was signed in 2021 and took effect in 2024. Negotiations with the European Union are ongoing but have been complicated by fundamental differences between US and EU privacy law.
The asymmetry is the critical point. Under CLOUD Act executive agreements, partner nations can request data from US companies — but only under conditions defined by the United States. Non-partner nations have no reciprocal access. And even partner agreements include limitations: they may not be used to target US persons, and they are subject to compliance requirements that the US unilaterally defines.
For the 190+ countries that are neither the United States nor one of its executive agreement partners, the practical reality is straightforward: their citizens’ data, stored on US cloud platforms, is accessible to US law enforcement through standard legal process. Their own governments have no equivalent mechanism to access data stored in the United States. The relationship is structurally one-directional.
III. Europe’s Rebellion: From GDPR to Sovereign Cloud
Europe has responded to this reality with a regulatory offensive that has, over the past eight years, fundamentally reshaped global data governance — even if it has not yet solved the underlying power imbalance.

The General Data Protection Regulation (GDPR), which took effect in May 2018, established the world’s most comprehensive framework for data protection and, crucially, asserted that EU citizens’ data rights follow the data regardless of where it is stored. GDPR’s extraterritorial reach was revolutionary: any company processing EU citizens’ data, anywhere in the world, must comply with EU privacy rules or face fines of up to 4% of global annual revenue.
But GDPR was designed to protect individual privacy, not national sovereignty. It constrains how data is used but does not determine where data resides or who can compel its production. The sovereignty question came into sharp focus in July 2020, when the Court of Justice of the European Union issued its landmark Schrems II ruling, invalidating the EU-US Privacy Shield — the legal mechanism that had allowed transatlantic data transfers — on the grounds that US surveillance laws did not provide adequate protection for EU citizens’ data.
The decision threw transatlantic data flows into legal limbo and exposed a fundamental tension: the EU was asserting that its citizens’ data deserved stronger privacy protections than US law provided, while US law simultaneously asserted the authority to access that data regardless of where it was stored or what protections had been promised.
The EU-US Data Privacy Framework, adopted in 2023, attempted to resolve this tension through executive commitments to limit US surveillance access to EU data. Privacy advocates like Max Schrems have publicly questioned whether the framework will survive legal challenge — and many expect a “Schrems III” ruling that could invalidate it as well.
Meanwhile, the October 2025 Cloud Sovereignty Framework represents a more fundamental shift. Rather than relying on legal agreements to constrain US data access, the EU is moving toward structural independence: building cloud infrastructure that is owned, operated, and governed within the EU, under EU law, beyond the jurisdictional reach of non-EU governments. The €180 million tender — to be awarded to up to four providers — requires compliance with eight sovereignty objectives spanning strategic, legal, operational, environmental, supply chain, technological, security, and regulatory domains.
“This is an extremely positive development for all those communities, organisations and companies that have invested time and resources in recent years in building sovereign structures,” the Sovereign Cloud Stack initiative noted in its analysis of the Framework.
IV. The Global South: Where Data Colonialism Hits Hardest
If Europe’s data sovereignty concerns are driven by legal asymmetries and geopolitical positioning, the Global South faces a more elemental version of the same problem: the wholesale extraction of data by foreign corporations from populations that derive almost no benefit from the transaction.
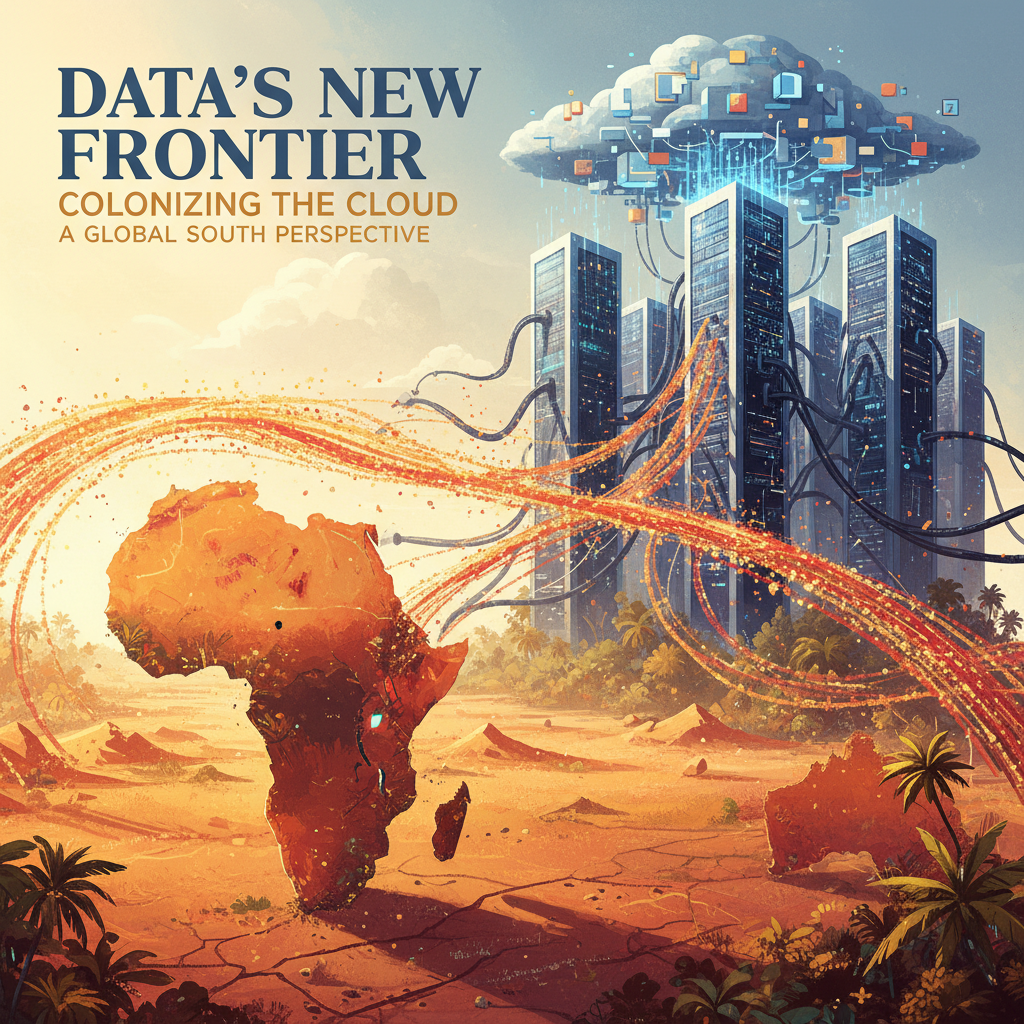
Michael Kwet, a researcher at Yale Law School, has documented what he calls “digital colonialism” — a system in which Big Tech firms, alongside state-backed digital infrastructure from the US and China, reshape the Global South through platforms, cables, and data flows. The mechanism echoes historical colonialism: extract raw materials (data) from peripheral nations, process them in metropolitan centers (Silicon Valley, Shenzhen), and sell the finished products (targeted advertising, AI models, surveillance tools) back to the source populations at a premium.
Facebook’s “Free Basics” program offers perhaps the most illustrative example. Launched across multiple African and Asian countries, Free Basics provided free internet access — but only to a curated selection of services within Facebook’s ecosystem. Critics argued it amounted to a digital enclosure: locking millions of new internet users into a walled garden that funneled their data to Facebook while starving local content creators and competitors of traffic and revenue. India banned the program in 2016, calling it a violation of net neutrality.
China presents a parallel but distinct model. Through its Digital Silk Road initiative, Chinese companies — particularly Huawei, ZTE, and Alibaba Cloud — have built telecommunications infrastructure, smart city systems, and cloud platforms across Africa, Southeast Asia, and Central Asia. In more than 50 African cities, Huawei has installed “Safe City” surveillance systems that integrate cameras, facial recognition, and data analytics platforms. The data generated by these systems is processed on Huawei infrastructure, raising questions about Chinese government access that mirror the CLOUD Act concerns regarding US providers.
The result is a form of digital dependency that maps disturbingly well onto historical patterns of colonial extraction. Raw data — the behavioral traces, medical records, financial transactions, and communications of billions of people — flows outward from the Global South to processing centers in the Global North (or China), where it is transformed into economic value that accrues almost entirely to foreign corporations and governments.
V. The USTR Reversal: America’s Changing Stance on Data Flows
For decades, the United States championed “free flow of data” as a core principle of international trade policy. The logic was straightforward: US technology companies dominate global digital services, and any restriction on cross-border data flows is, functionally, a trade barrier against American industry.

This principle was embedded in trade agreements. The Trans-Pacific Partnership (TPP) included provisions prohibiting data localization requirements and mandating free cross-border data flows. The United States-Mexico-Canada Agreement (USMCA) contained similar provisions. The “Digital Dozen” — a set of principles adopted by the US Trade Representative (USTR) under the Obama administration — explicitly listed cross-border data flow protection and opposition to data localization as core US negotiating objectives.
Then, in October 2023, the USTR did something unexpected: it withdrew support for provisions on cross-border data flows, data localization, and transfer of source code in the Joint Statement Initiative on E-commerce at the WTO. The reversal stunned trade policy observers and Silicon Valley alike.
The reasons were complex. Domestically, growing bipartisan concern about Big Tech’s power had eroded political support for policies perceived as protecting tech companies’ global business models. Lawmakers increasingly recognized that opposing all data localization requirements made it harder for the US itself to regulate tech platforms or protect Americans’ data. And the rise of AI — which depends on massive training datasets — had introduced new considerations about whether unrestricted data flows might disadvantage US interests by allowing foreign competitors to train models on American data without reciprocal access.
The shift also reflected a broader geopolitical recalibration. As digital infrastructure became a contested domain between the US and China, the simplistic equation of “free data flows = American advantage” gave way to more nuanced calculations about who benefits from which data moving where.
The result is a global vacuum: the United States has withdrawn from actively promoting its data flow principles, but no consensus alternative has emerged. Individual nations and regional blocs are filling the void with a patchwork of localization requirements, sovereignty frameworks, and bilateral agreements — creating a fragmented digital landscape that serves no one’s interests efficiently.
VI. The Balkanization Dilemma: What Happens When Data Can’t Move
Data sovereignty advocates face a genuine tension: the more effectively you restrict data flows to protect sovereignty, the more you fragment the global digital infrastructure that enables modern medicine, science, commerce, and communication.
Consider clinical genomics — the field that makes treatments like KJ Muldoon’s personalized CRISPR therapy possible. Rare disease diagnosis depends on matching a patient’s genetic sequence against global databases. A patient in Bogotá with an undiagnosed condition may have a mutation that has been characterized only in a research database in Finland. If data localization requirements prevent the patient’s sequence from leaving Colombia, or prevent the Finnish database from being accessible across borders, the diagnosis never happens.
The same tension applies to pandemic surveillance, climate modeling, global financial systems, and virtually every domain where the value of data increases with aggregation and cross-referencing. Data localization, taken to its logical extreme, produces a world of information islands — each sovereign, each isolated, each less capable than the connected whole.
The challenge, then, is not to choose between sovereignty and connectivity, but to build architectures that enable both. This requires infrastructure that allows data to be shared without being surrendered — systems where the data owner retains control over access permissions, usage terms, and deletion rights regardless of where the data is processed or by whom.
Traditional centralized cloud architectures are poorly suited to this model because they inherently concentrate control in the infrastructure provider. When your data lives on Amazon’s servers, Amazon’s compliance with access requests — whether from your government, the US government, or a court in any jurisdiction — is determined by Amazon’s policies and legal obligations, not yours.
VII. The Decentralized Alternative: Data Sovereignty Without Data Isolation
The structural answer to the sovereignty-versus-connectivity dilemma may lie in decentralized architectures — systems designed from the ground up to separate data storage from data control, allowing information to flow across borders while keeping sovereignty with the data owner.
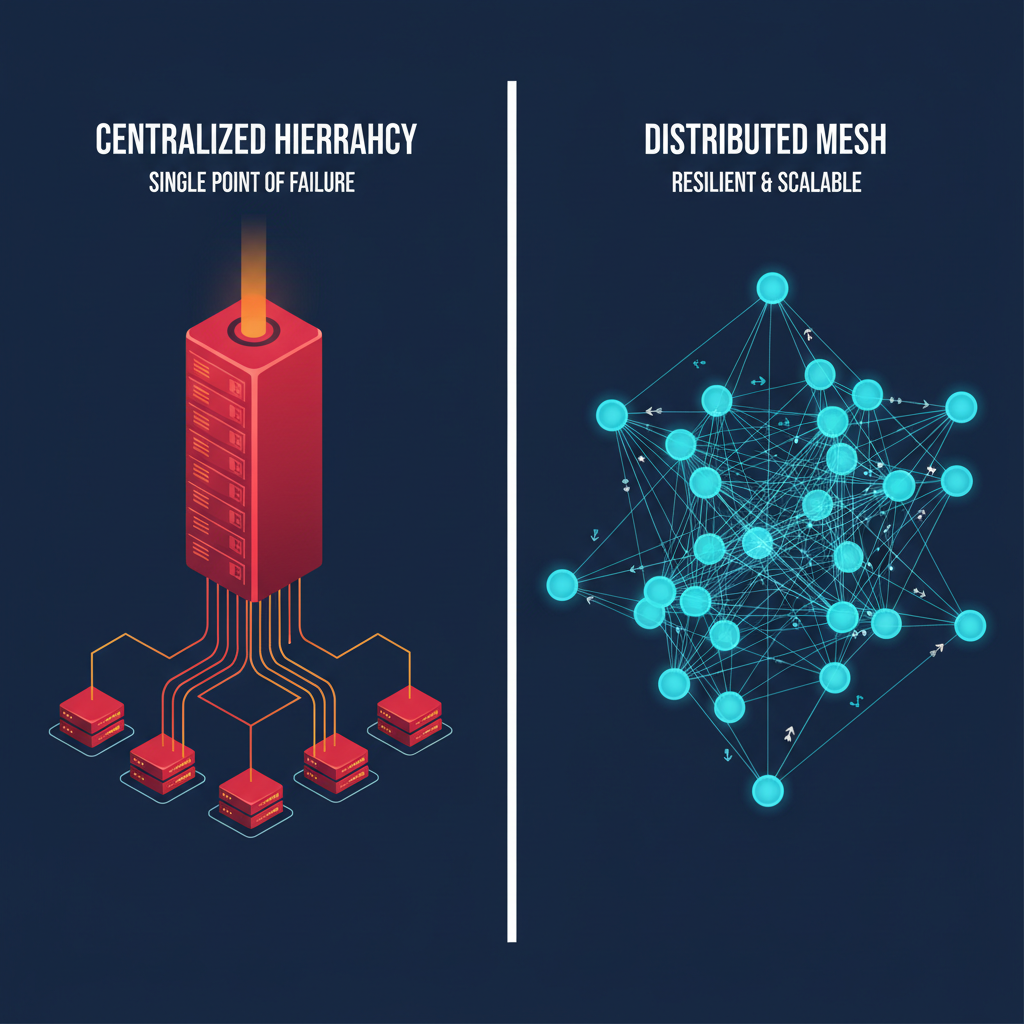
The concept is not new. BitTorrent demonstrated decades ago that data could be stored and transmitted without a central server. IPFS (the InterPlanetary File System) provides decentralized, content-addressed storage where files are identified by their cryptographic hash rather than their physical location. Blockchain-based systems offer immutable audit trails for data access and modification.
What is new is the maturity of these systems and the growing recognition that they address a genuine policy need. When the European Commission’s Cloud Sovereignty Framework talks about “supply chain transparency” and “technological openness,” it is describing properties that are intrinsic to decentralized architectures and difficult to achieve with centralized ones.
Platforms like GRIDNET OS exemplify this approach — offering decentralized storage, crypto-incentivized data exchange, and decentralized user-facing applications that give end users (patients, doctors, citizens) direct control over their data without relying on a single cloud provider subject to foreign jurisdiction. The persistent storage layer ensures that data remains available regardless of any single node’s status, while the decentralized application framework means that the interfaces people use to access their data aren’t controlled by a single corporate entity.
The vision is compelling: a global data infrastructure where sovereignty follows the data owner, not the data center. Where a hospital in Lagos can share patient records with a specialist in Munich through an encrypted, permissioned channel that neither Amazon nor the NSA can intercept. Where a government can ensure that its citizens’ data is subject to its own laws without disconnecting from the global digital economy.
Whether decentralized systems can achieve the performance, reliability, and ease of use required for mainstream adoption remains an open question. But the architectural principles — separation of storage from control, encryption by default, user-controlled access permissions, and jurisdictional independence — align precisely with the sovereignty requirements that governments worldwide are increasingly demanding.
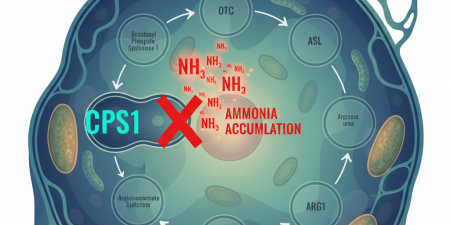
VIII. The Medical Frontier: Where Data Sovereignty Becomes Life or Death
The stakes of data sovereignty become most visceral in healthcare, where the data in question is not browsing history or purchase records but genetic sequences, diagnostic imaging, treatment histories, and the intimate biological details that define a patient’s medical reality.

The EU Cloud Sovereignty Framework was motivated, in significant part, by healthcare concerns. European hospitals increasingly use cloud-based electronic health record systems, many of which are provided by US companies. Diagnostic AI tools — trained on patient data from multiple countries — process medical images and genomic sequences on cloud infrastructure that may span jurisdictions. The result is that a European patient’s most intimate medical data may be stored on US servers, processed by AI models trained on Chinese data, and accessible to law enforcement in multiple jurisdictions — all without the patient’s knowledge or meaningful consent.
The push for healthcare data sovereignty is not hypothetical. Germany’s Gaia-X initiative, France’s Health Data Hub controversy (which erupted when it was revealed that French health data was being hosted on Microsoft Azure), and Estonia’s pioneering X-Road system (which provides a decentralized data exchange layer for all government services, including healthcare) all reflect the growing consensus that medical data demands special sovereignty protections.
For the emerging field of personalized medicine — where treatments like KJ Muldoon’s CRISPR therapy depend on the precise characterization of individual genetic mutations — the data sovereignty question is particularly acute. A patient’s genome is the most uniquely identifying piece of data in existence. It cannot be anonymized (any sufficiently large genomic dataset can be re-identified). It reveals information not only about the patient but about their family members. And it has indefinite relevance — unlike a credit card number, a genome cannot be changed if compromised.
Building the genomic data infrastructure for personalized medicine in a way that respects patient sovereignty, enables cross-border diagnostic matching, and resists both corporate exploitation and government overreach is one of the defining technical challenges of the next decade. The answer will shape not only data policy but health outcomes for billions of people.
IX. The Emerging Consensus: Sovereignty as Architecture, Not Just Policy
After years of patchwork responses — a regulation here, a localization law there, a trade agreement exception somewhere else — a more coherent vision of data sovereignty is beginning to emerge. Its core principle: sovereignty must be embedded in the technical architecture of data systems, not merely imposed through legal frameworks that operate on top of architectures designed for extraction.
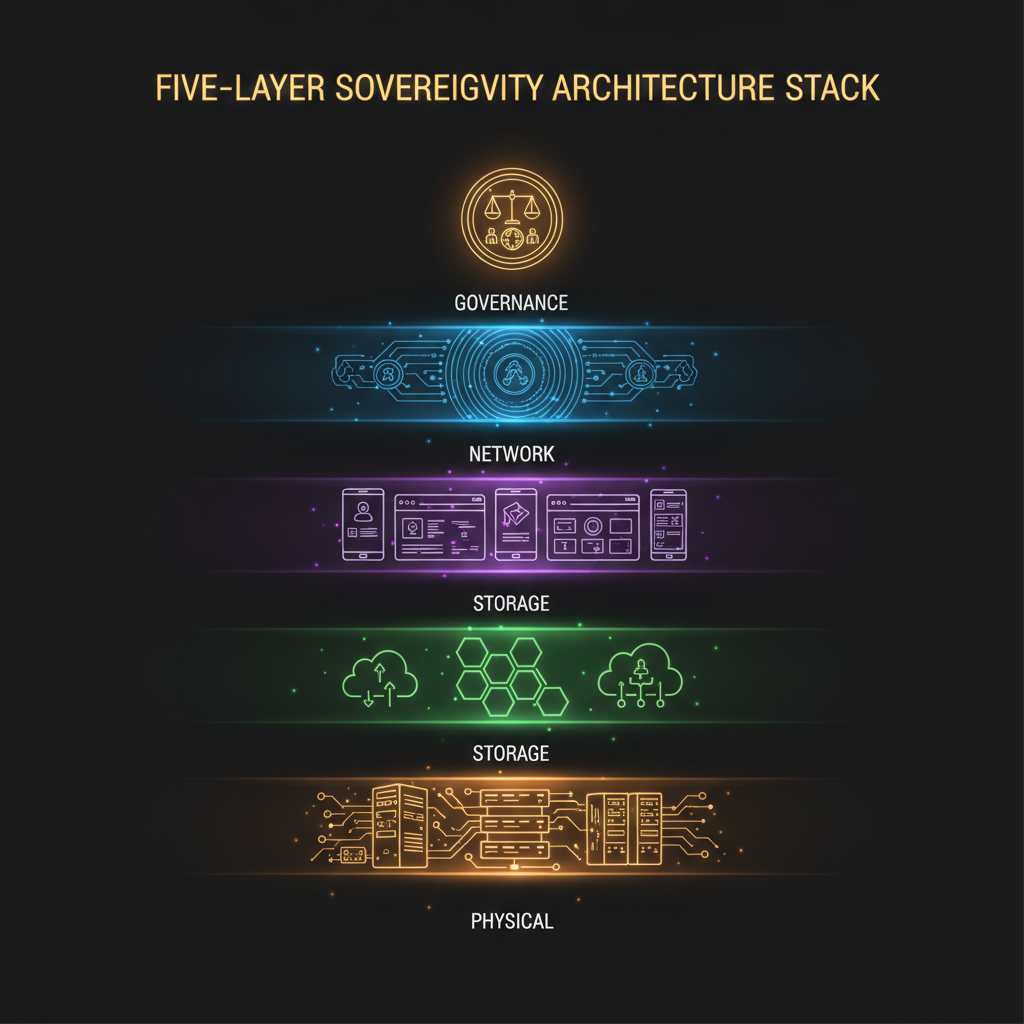
This represents a fundamental shift in thinking. GDPR, the CLOUD Act, and their equivalents are legal instruments — they define who should be allowed to do what with data. But legal instruments are only as strong as the enforcement mechanisms behind them, and in a world where data physically resides under a foreign jurisdiction, enforcement often means asking the jurisdiction that controls the data to comply with rules it didn’t write and may not agree with.
Architectural sovereignty means designing systems where the technical properties of the infrastructure enforce sovereignty guarantees regardless of the legal environment. Encryption ensures that data is unreadable without the owner’s key, regardless of who controls the physical server. Decentralized storage ensures that no single jurisdiction controls a complete copy of any dataset. Cryptographic access logging ensures that any data access — by a doctor, a researcher, or a government agency — is immutably recorded and auditable.
The EU’s Cloud Sovereignty Framework points in this direction. Its requirements for “technological openness,” “supply chain transparency,” and “compliance with EU laws” are most naturally satisfied by open-source, decentralized systems where the architecture itself provides the guarantees that contracts and regulations can only promise.
The nations and organizations that build or adopt such infrastructure first will define the terms of digital sovereignty for the next generation. Those that don’t will find themselves negotiating from a position of permanent dependency — writing laws about data they don’t control, stored on infrastructure they don’t own, under jurisdictions they can’t influence.
X. The Road Ahead: Three Futures
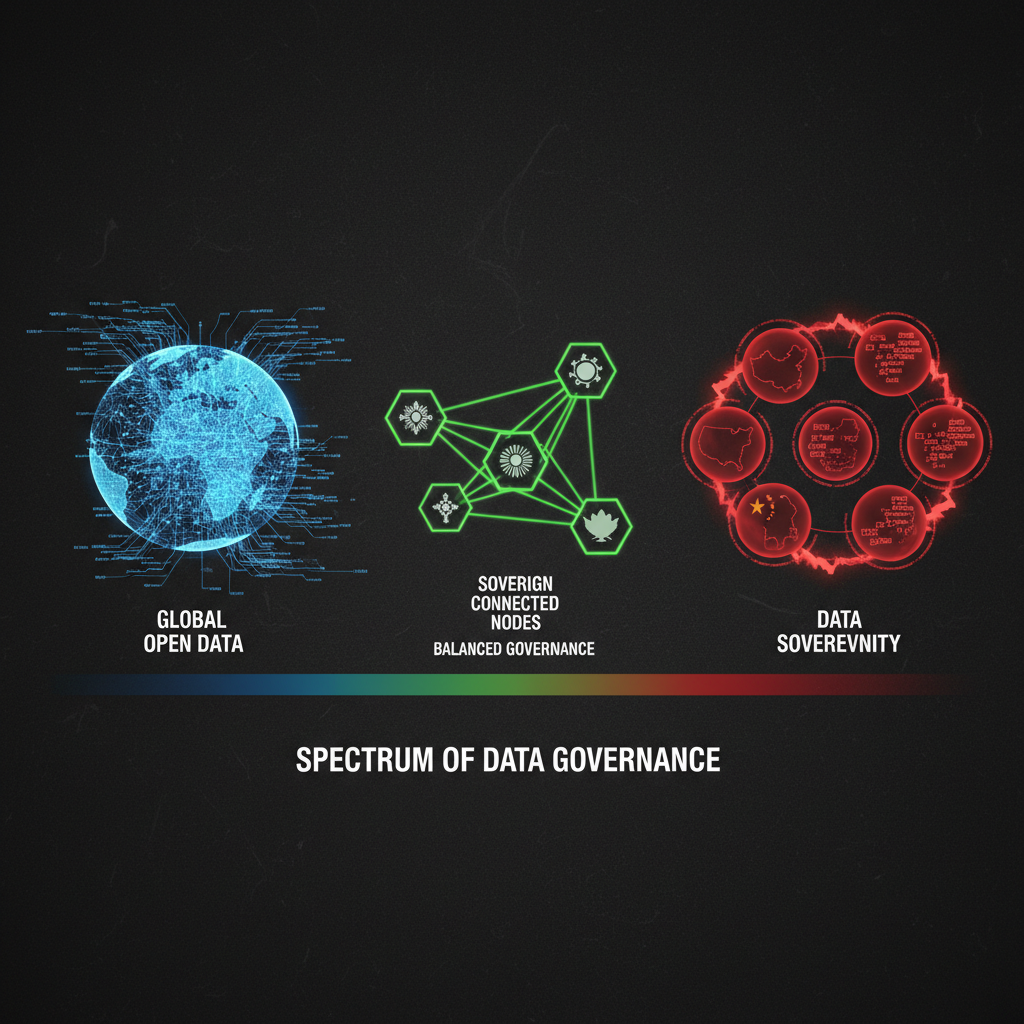
The global data sovereignty landscape is heading toward one of three scenarios, and the outcome will shape international relations, economic power, and individual rights for decades.

Scenario 1: Continued Dominance. US and Chinese cloud providers continue to consolidate global market share. Data sovereignty concerns are managed through bilateral agreements and regulatory accommodations, but the fundamental power asymmetry persists. The Global South remains digitally dependent, and sensitive data — medical, financial, governmental — continues to reside under foreign jurisdiction. This is the path of least resistance, and it is the most likely outcome absent deliberate intervention.
Scenario 2: Fragmented Balkanization. Nations increasingly require data localization, building national cloud infrastructures that don’t interoperate. Global digital services fragment along national borders. The benefits of cross-border data exchange — for science, medicine, commerce, and communication — diminish. Innovation slows as datasets shrink to national scale. Authoritarian regimes use sovereignty rhetoric to justify surveillance. This is the worst-case outcome, and current trends in Russia, China, and parts of South Asia suggest it is already partially materializing.
Scenario 3: Federated Sovereignty. Decentralized architectures enable data to flow across borders while sovereignty remains with data owners. Open protocols replace proprietary platforms. Encryption and cryptographic access control provide sovereignty guarantees that don’t depend on trusting any single provider or government. Global digital services continue to function, but the infrastructure layer becomes distributed, transparent, and jurisdictionally neutral. This is the most technically demanding outcome, but it is the only one that resolves the sovereignty-connectivity tension without sacrificing either value.
The technology for Scenario 3 exists. The policy demand for it is growing. The question is whether the political will, investment, and institutional coordination needed to build it can materialize before the momentum of Scenarios 1 and 2 becomes irreversible.
The new colonialism has no flags, no armies, and no treaties. It operates through terms of service, cloud infrastructure agreements, and the quiet assumption that the nation hosting the data gets to write the rules. For billions of people, the most intimate details of their lives — their health records, their financial transactions, their communications, their genetic codes — are stored under a jurisdiction they didn’t choose, governed by laws they didn’t write, accessible to authorities they can’t hold accountable.
Data sovereignty is not an abstract policy debate. It is the defining question of who holds power in the digital age. And the answer is being written now — in procurement frameworks and trade agreements, in regulatory guidance and technical architectures, in the choice between infrastructure that serves its owners and infrastructure that serves its operators.
The question is not whether data sovereignty matters. The question is whether the nations and peoples who need it most will have the tools to claim it.
References & Sources
- European Commission (2025). “Cloud Sovereignty Framework.” Version 1.2.1, October 20, 2025. commission.europa.eu
- European Commission (2025). “The Commission moves forward on cloud sovereignty with a EUR 180 million tender.” October 10, 2025. commission.europa.eu
- CMS Law (2026). “White Paper: Demystifying the debate on the US CLOUD Act vs European/UK Data Sovereignty in the context of cloud services.” February 2026. cms-lawnow.com
- Wire (2025). “CLOUD Act – What It Means for EU Data Sovereignty.” August 14, 2025. wire.com
- Orrick (2026). “Data Localization and the Sovereign Cloud: EU Cloud Regulations Explained.” January 2026. orrick.com
- Kwet, M. (2019). “Digital Colonialism: US Empire and the New Imperialism in the Global South.” Race & Class, 60(4), 3-26. DOI: 10.1177/0306396818823172
- Modern Diplomacy (2025). “Digital Colonialism: How Data Empires Are Rewriting Global Sovereignty.” June 6, 2025. moderndiplomacy.eu
- Congressional Research Service (2024). “Digital Trade and Data Policy: Key Issues Facing Congress.” congress.gov
- Lawfare (2025). “The U.K.-U.S. Data Access Agreement.” June 20, 2025. lawfaremedia.org
- Cross-Border Data Forum (2025). “CLOUD Act: Answers to Frequently Asked Questions.” July 2025. crossborderdataforum.org
- Sovereign Cloud Stack (2025). “The EU Commission’s Cloud Sovereignty Framework.” October 29, 2025. sovereigncloudstack.org
- CISERO (2025). “The EU Cloud Sovereignty Framework: Context, Relevance and Perspectives from the IPCEI-CIS Ecosystem.” cisero-project.eu
- Court of Justice of the European Union (2020). Case C-311/18 (Schrems II). July 16, 2020.
- United States Congress (2018). “Clarifying Lawful Overseas Use of Data Act (CLOUD Act).” H.R. 4943, signed March 23, 2018.
- The Sunday Diplomat (2025). “Digital Colonialism: How Tech Powers Are Rewriting Africa’s Sovereignty.” November 8, 2025. thesundaydiplomat.com